Lets Encrypt
Overview
Let's Encrypt is a free certificate authority. It allows to issue TLS (HTTPS) certificate for any website. If you need in depth introduction to this topic please refer to docs. Let's Encrypt Documentation
In this documentation we present basic architecture for generating a certificate for your domains over HTTP challenge. There are also other methods of authentication LIKE DNS challenge which allows to create wildcard certificates for non www. sites.
Legal information
Let's encrypt, LEGO, Certbot are not owned or developed by GSD-Software. Our documentation is only a rough concept of basic environment that can be used to generate valid certificates. If you have any problem with the software mentioned above please refer to the official documentation.
Requirements
- Opened port 80
- Proxy server [nginx/apache/GSDProxy]
- Possibility to schedule tasks (Windows: scheduler, Unix: cron)
How to use
Disclaimer
This documentation does not go into details, may contain simplified terminology and have minor discrepancies towards official documentation. In order to get full scope of information, please check Let's Encrypt Documentation
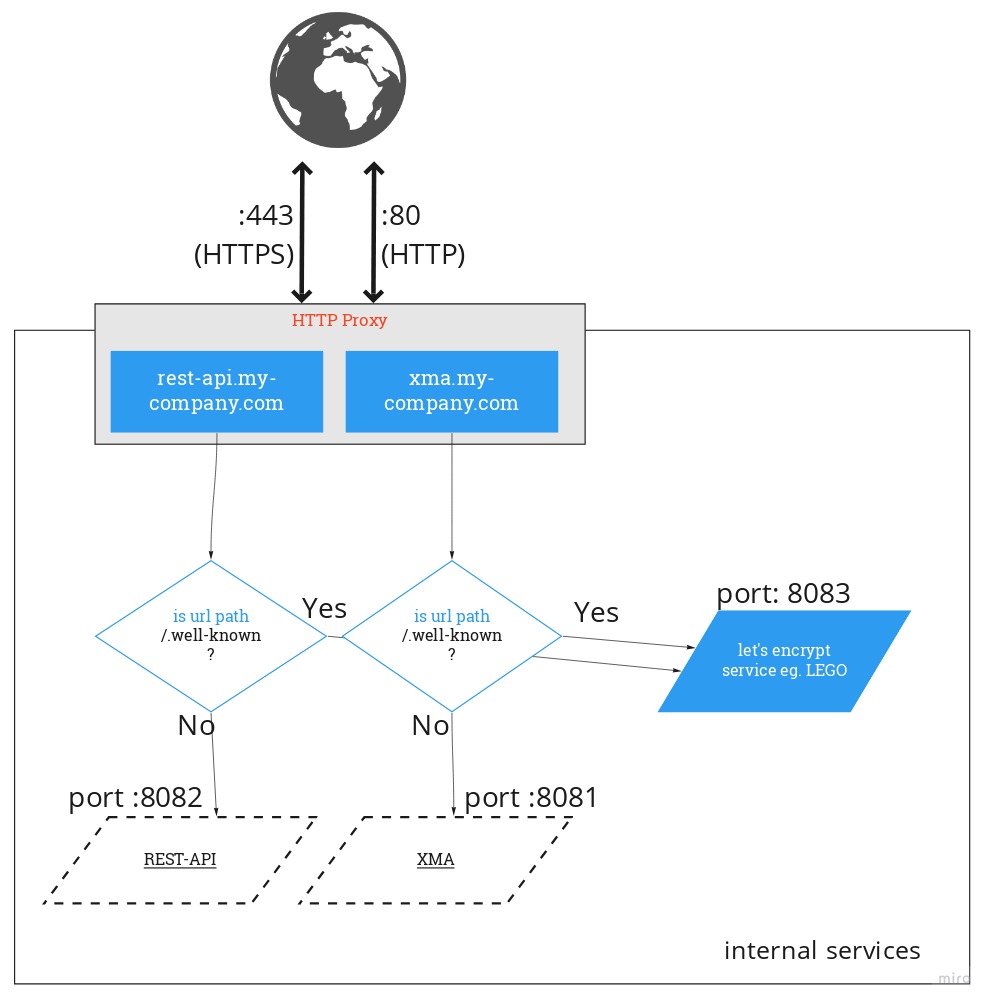
Here is the architecture you can refer to when you want to introduce let's encrypt certificates in your company.
We use most common way of authenticating domain owner which is HTTP request. We recommend using LEGO as the let's encrypt certificate request service, it's open source and cross platform application. You can download it here: LEGO Executables
In order to get certificate you should have :80 port opened and redirect request which contains "/.well-known" path to the LEGO.
For first use of lego you must request new certificate. You can do it by running following command in your console (cmd.exe or linux shell).
lego --email="foo@bar.com" --domains="example.com" --http run
Port 80
This command will bind on port 80 which requires proper permissions. It may also collide with your proxy server. You can change default port on which
LEGO binds by using --http.port {YOUR DESIRED PORT} parameter. Remember that you must forward HTTP connection to this port in your proxy application.
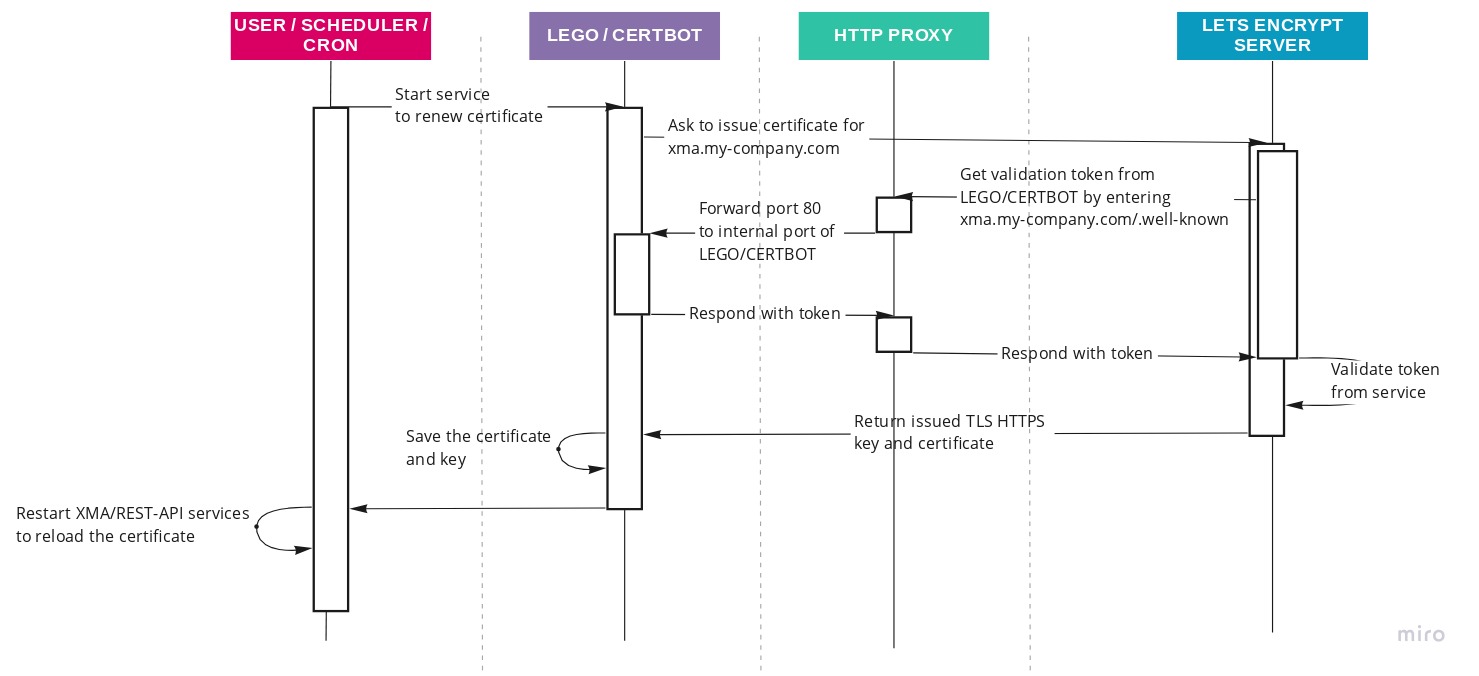
After running this command, LEGO will ask let's encrypt servers to check if you are the owner of such domain. To do so, the authority will try to make
request to your domain on example.com/.well-known. Your proxy must forward this request to LEGO which will return validation token. If this workflow
runs properly valid certificates will be saved under .lego directory in working directory.
Here is how this process looks like
Renew certificate
Your newly created certificate is valid for 90 days. Let's encrypt allows to renew the certificate 30 days before the expiration date. You can renew
your cert by running lego --email="foo@bar.com" --domains="example.com" --http renew command.
Because this process is repeatable you should automate it.
Windows
Here is the basic *.bat script you can begin from.
1 2 3 | CD /<your drive letter> <full path to GSD application> START <path to lego>/lego.exe --email="<your email>" --domains="<your domain>" --http renew NET stop <service name> && NET start <service name> |
Save this script as *.bat file, change the variables then add it to monthly schedule in Windows Scheduler.
Linux
Running renew command on linux requires cron to be installed. Then create following script:
1 2 3 | cd "<full path to GSD application>" <path to lego>/lego --email="<your email>" --domains="<your domain>" --http renew supervisorctl restart "<service name>" |
save it and add permissions for executing chmod a+x <path to your script>.
Now you can add following rules to cron, run sudo crontab -e and add following entry:
0 0 1 */2 * <path to your script>
where 0 0 1 */2 * means -> At 00:00 on day-of-month 1 in every 2nd month.